To protect data in the age of quantum computers, engineers propose a new type of encryption. It’s reasonable to believe that an encrypted email cannot be read by prying eyes. That’s because, unless you’re the intended recipient, you’d need the answer to a mathematical problem that’s nearly impossible for a computer to solve in a reasonable amount of time in order to break through most of the encryption systems we use on a daily basis.
At least for modern computers, it’s nearly impossible.
“If quantum computing becomes a reality, however, some of those problems are not hard anymore,” said Shantanu Chakrabartty, the Clifford W. Murphy Professor and vice dean for research and graduate education in the Preston M. Green Department of Electrical & Systems Engineering at the McKelvey School of Engineering.
These new computing paradigms are already becoming a reality and may soon be deployable. Hackers are already preparing by storing encrypted transactions in the hope of deciphering the information later.
Chakrabartty’s lab at Washington University in St. Louis proposes a security system that is not only resistant to quantum attacks, but also cheap, convenient, and scalable without the need for expensive new equipment.
If quantum computing becomes a reality, however, some of those problems are not hard anymore. A big vulnerability would be if you could tap into the power source. You would be able to monitor the fluctuations in power consumption to get secret information.
Shantanu Chakrabartty
Security is often managed today by key distribution systems in which one person sends information hidden behind a key, maybe a long string of seemingly unassociated numbers. The receiver of that information can access the information if they possess another specific key. The two keys are related in a mathematical way that is nearly impossible to guess, but can be easily solved with the right algorithm or using a quantum computer.
There have been potential solutions for securing data against a “quantum attack.” Some technologies have been commercialized already. But they are computationally very expensive or require dedicated optical fibers or satellite links via lasers.
The new protocol for Symmetric Key Distribution, which Chakrabartty and Mustafizur Rahman, a PhD student in Chakrabartty’s lab and first author on the research paper, refer to as SPoTKD, doesn’t require lasers or satellites or miles of new cable. It relies on tiny microchips embedded with even tinier clocks that run without batteries.

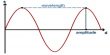
The clocks are really electrons that seem to magically transport themselves between two locations on the chip using quantum tunneling; the “time” refers to the motion of the electrons. When the chips are created, their initial state is also recorded on a computer server.
If someone wants to create a secure channel, they note the time on a subset of the clocks and send that information to the server, which can use its knowledge of the initial state to determine what time the clocks read at the time they were sent. The server lets the person know what the times were and, if correct, a secure channel of communication has been opened.
The quantum nature of electron transport adds some extra layers of security; if they are measured, the clock collapses. It will vanish forever, and neither a spy nor the recipient will be able to access the data.
And, as Chakrabartty has demonstrated in the past, these systems can also power themselves for extended periods of time with the smallest initial energy input, thanks to quantum tunneling properties. Another security advantage of his SPoTKD is that it is not powered by outside energy.
“A big vulnerability would be if you could tap into the power source,” Chakrabartty said. “You would be able to monitor the fluctuations in power consumption to get secret information.”
Chakrabartty is developing additional features for these chips, such as the ability to self-destruct after a set period of time. The Office of Technology Management has filed a provisional US patent for the technology.
SPoTKD could eventually be used to ensure that medical records are destroyed after being read by a doctor, or to enforce time limits on software licenses. They can protect voting records, validate NFTs, or simply ensure that no one is reading your email.